
“Being in the community banking industry for nearly 20 years, I have built many great relationships with customers and many of them I now call friends. Beginning my career in Wyoming, I was tasked to assist the CFO/CIO with many IT/IS services which sparked my interest in business technology. I will assist in finding solutions to provide the services necessary to keep your bank efficient and secure.”
Contact us if you have questions regarding policy/regulation updates, vulnerability/penetration tests, and social engineering.
Contact us for more information
Every month, some new cybersecurity or information security issue reminds of the extreme importance it is to be prepared for anything! From major global impacts caused by a software update to the most basic forms of malware. See below all the different ways CivITas Bank Solutions is here to protect your community bank and allow you the time and focus to provide service where it matters most...with your customers.

Consulting
Security expertise from your IT committee; review of policies, contracts, and vendors; assistance with project management.
Want more information?Phishing Tests
Training-based approach to reduce the risk of ransomware, data loss, and Business Email Compromise.
Want more information?

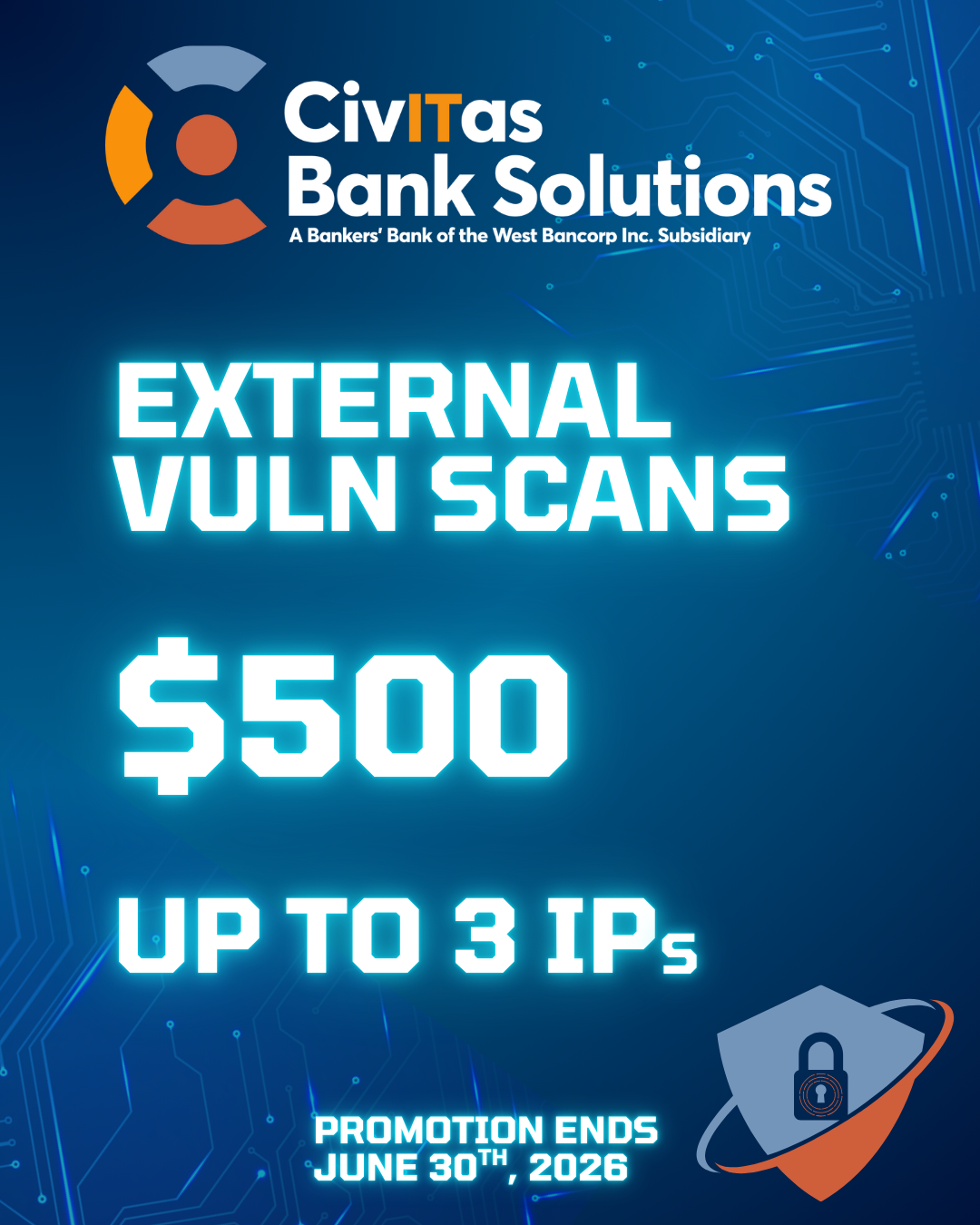
Vulnerability Management
Security assessments and penetration tests to prioritize the network risk in your environment and shore up defenses.
Want more information?Security Monitoring
Provide 24/7/365 visibility into security events on your network, with the power of human analysts escalating incidents.
Want more information?

